Embedded and IoT cable-connected devices running Microsoft's Windows 10 IoT Core are exposed to remote command execution attacks with SYSTEM privileges that require no authentication, with the help of an open source RAT tool released on GitHub.
Windows 10 IoT Core-powered devices run a version of Windows 10 optimized for smaller ARM and x86/x64 devices, compatible with universal apps and drivers but with no support for shells or Microsoft apps.
The SirepRAT tool developed by SafeBreach's Dor Azouri is designed to exploit the Sirep test service built-in "on any cable-connected device running Windows IoT Core with an official Microsoft image."
As the researcher told BleepingComputer:
It is important to note that there are 2 editions of this OS: one is IoT Core, which is aimed for simpler IoT solutions, and the other is IoT enterprise, which serves more complex scenarios. The former is free and supports ARM, the latter is paid and supports only x86_64 chips. I have only tested this attack on IoT Core, with the default image provided by Microsoft. Microsoft states in their documentation that manufacturers/OEMs that seek to commercialize their products, must build their own custom image, with all of the test packages left out.
Only cable-connected devices are exposedThe good news is that the SirepRAT Windows 10 IoT Core exploitation tool released by the researcher on GitHub will only work via an Ethernet connection because the less-known interface it exposes is "used by HLK for driver/HW tests" over wired connections.
"The research was performed on a Windows IoT Core installed on a Raspberry Pi 3, but is probably not limited to this board as it abuses a Windows service and protocol, which should be platform independent," also says Azouri.
As determined by a survey sponsored by The Eclipse IoT Working Group, AGILE IoT, IEEE, and the Open Mobile Alliance, and cited by the researcher in his paper:
Windows has the second largest (22.9%) share in IoT solutions development (after Linux, 71.8%).
One of the major IoT sectors in which Windows is used is IoT gateways.
A large share of the IoT solutions in development is built on top of ARM architecture.
Security is the top concern for developing IoT solutions.
Exploiting the devices requires no authentication"This service is the client part of the HLK setup one may build in order to perform driver/hardware tests on the IoT device. It serves the Sirep/WPCon/TShell protocol," according to Azouri. "We broke down the Sirep/WPCon protocol and demonstrated how this protocol exposes a remote command interface for attackers, that include RAT abilities such as get/put arbitrary files on arbitrary locations and obtain system information."
Azouri told BleepingComputer that "This is a test interface that is enabled and running by default on the official stock images provided publicly by Microsoft. Unless this feature is removed by building a custom image (a process that requires purchasing certificates from a CA and thus is unlikely to be done by most users), the device is prone to this attack by anyone who has a TCP connection to the device, on the Sirep service's port."
A source familiar with the Windows 10 IoT Core OS stated that the test images will display the following warning when booting up: "This is a Windows 10 IoT Core test image designed for prototyping only. If you are looking to commercialize, you must use a custom FFU for optimal security."
The devices which can be exploited with the help of SirepRAT can be found in a multitude of environments, from commercial handheld products and DIY projects to enterprise environments.
As detailed in the research, "The achieved execution can be performed as either the SYSTEM user or the currently logged on user (usually DefaultAccount), without any needed authentication.
From SirepRAT's source code released on GitHub by the researcher, the RAT tool can launch commands on compromised devices without any output, upload and download files, as well as exfiltrate file and system information.
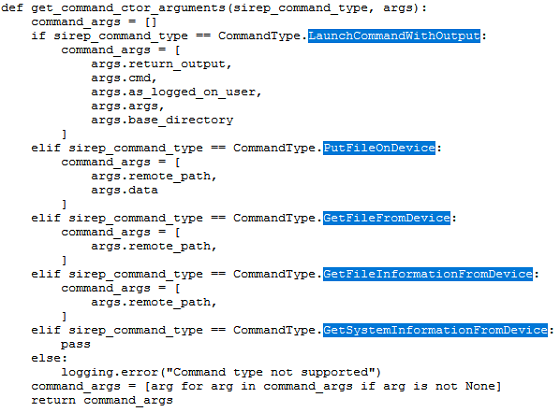 SirepRAT commands
SirepRAT commandsGiven that the SirepRAT utility created by Azouri makes it simple for attackers to bypass authentication and freely upload/download files to arbitrary locations, taking over vulnerable devices using Azouri's RAT tool is more than likely, leading to possible large scale attacks against Windows IoT Core devices.
Full information on how to exploit Windows 10 IoT Core devices for remote command execution with SirepRAT utility is available on the
project's Github page.
The "
SirepRAT: RCE as SYSTEM on Windows IoT Core" paper was presented by Dor Azouri at the WOPR Summit hacking conference on Saturday.
BleepingComputer has reached out to Microsoft for comment but had not heard back by the time of this publication. This article will be updated when a response is received.
Update March 04 2019 15:15 EST: Added the Windows 10 IoT Core OS test image boot up prototyping warning.
source