Microsoft has announced today that the Windows 10 Tamper Protection security feature is now officially generally available for the Enterprise and consumers. Along with this announcement, Microsoft will be enabling this security feature on all Windows 10 devices by default.
Tamper Protection is a security feature that was introduced in Windows 10 version 1903, otherwise known as the May 2019 Update. When enabled, Tamper Protection prevents Windows Security and Windows Defender settings from being changed by programs, Windows command line tools, Registry changes, or group policies.
Instead, users must modify security settings directly through the Windows 10 user interface or via Microsoft enterprise management software such as Intune.
If Tamper Protection is not currently enabled on your Windows 10 device, Microsoft has told BleepingComputer that they will be rolling out this change to all Windows 10 users. It may take a few days, though, before it becomes enabled automatically for everyone.
If you do not want to wait, you can enable it now,
by following these instructions.
Tamper Protection is an important tool to prevent security bypassesWith the Windows Defender becoming a reliable antivirus solution and further security enhancements being added to Windows 10, malware has increasingly made efforts to bypass it.
This is done by attempting to turn off or reduce the functionality of Windows Defender through PowerShell commands, group policies, or Registry modifications.
For example, over the past 4 months we have seen TrickBot, GootKit, and the Nodersok Trojans make a concerted effort to bypass Windows Defender in order to remain resident on an infected computer or to bypass its protections.
 TrickBot disabling Windows Defender protections
TrickBot disabling Windows Defender protectionsWith Tamper Protection enabled, though, these attempts to change Windows Defender or Windows Security settings will be ignored or simply reset.
As Windows Defender automatically turns on when a third-party antivirus software is removed, it is even more important to enable Tamper Protection so that Windows Defender can adequately protect you.
Consumers use the Windows Security settingsFor consumers, Tamper Protection is managed under the Virus & Threat Protection settings in Windows Security.
To access this, you would open the Windows 10 settings, click on
Windows Security, then
Virus & Threat Protection, and then click on
Manage Settings under Virus and Threat protection settings.
Scroll down and you will see an option titled Tamper Protection, which you should enable as seen below.
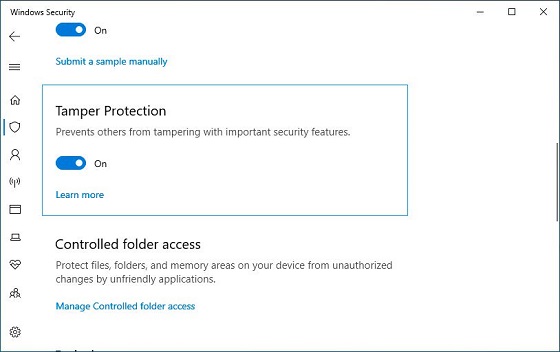 Managing Tamper Protection in Windows Security
Managing Tamper Protection in Windows SecurityWhile Enterprise workstations can enable Tamper Protection using the same method as consumers, administrators can also manage it using the Microsoft Intune management software.
Using Intune, an organization can enable Tamper protection for the entire org, by device types, or even user groups as shown below.
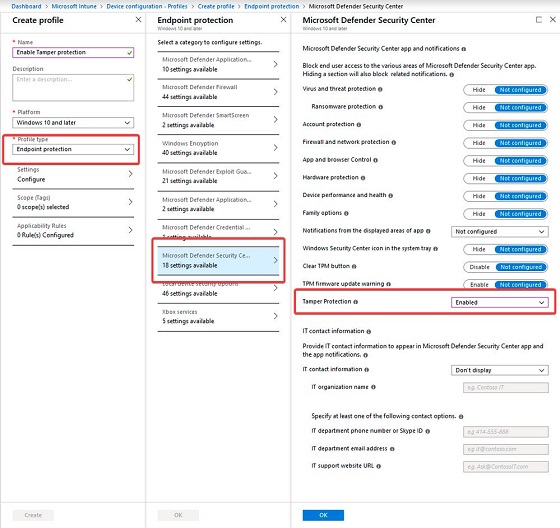 Managing Tamper Protection in Intune - Click image to see full size
Managing Tamper Protection in Intune - Click image to see full sizeWhen enabled via Enterprise software, workstations will show that this setting is being "managed by your administrator".
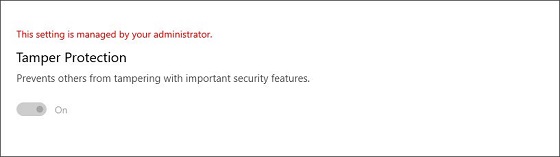 Managed by Admin
Managed by AdminTo provide additional security for Tamper Protection management, every time a change in Tamper Protection settings are pushed out by Intune, the request will be digitally signed.
When a workstation receives this request, they will confirm that the signature is legitimate, and if not, ignore the changes. You can see an illustration of how these signed requests are pushed out by Intune below.
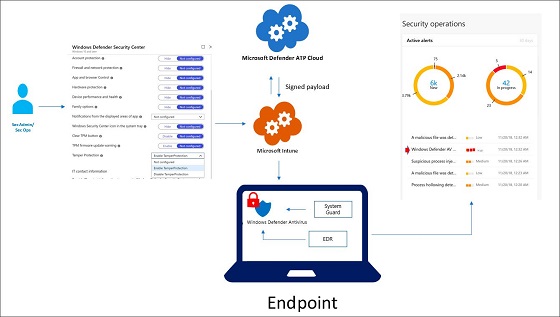 Microsoft Intune Signed Message
Microsoft Intune Signed MessageWhen an attacker, whether it be malware or a local user, attempts to tamper with Windows Security or Windows Defender settings, an alert will be pushed to Microsoft Defender Security Center. Administrators can then dig into these alerts to see what machine are being targeted and perform remediation.
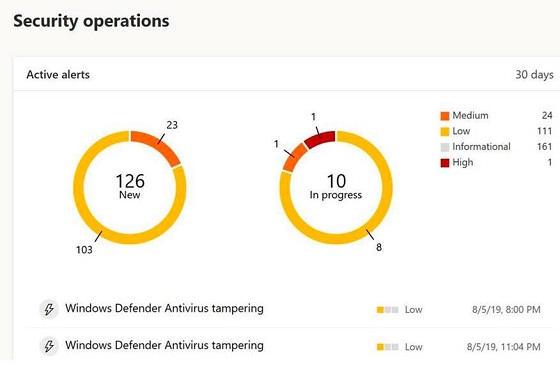 Tamper Protection Alerts in Microsoft Defender Security Center
Tamper Protection Alerts in Microsoft Defender Security CenterWith malware actively targeting Tamper Protection, this feature is not only important, but required to be enabled to provide complete protection to Windows 10 users.
All users, whether consumers or Enterprise organizations, should make sure to enable Tamper Protection.
source