A simple VBScript may be enough to allow users to gain administrative privileges and bypass UAC entirely on Windows 10.
In a new report from a PwC UK security researcher Wietze Beukema, we learn that almost 300 Windows 10 executables are vulnerable to DLL hijacking.
It turns out nearly 300 executables in your System32 folder are vulnerable to relative path DLL Hijacking. Did you know that with a simple VBScript some of these EXEs can be used to elevate such executions, bypassing UAC entirely? explained Beukema.
The vulnerability referred to here is relative path DLL hijacking, which is when an attacker can cause a legitimate Windows executable to load an arbitrary DLL of the attackers choice, most likely with malicious intent.
DLL hijacking attacks can prove useful to a skilled attacker as they grant capabilities such as arbitrary code execution, privilege escalation, and persistence on the target system.
The various techniques of DLL hijacking covered by the Beukema's blog post include DLL replacement, DLL Proxying, DLL search order hijacking, Phantom DLL hijacking, DLL redirection, WinSxS DLL replacement, and relative path DLL Hijacking.
A working exampleTo demonstrate relative path DLL hijacking in practice, Beukema focused on the libraries present in the C:\Windows\System32 folder on a Windows 10 (v1909) machine.
He copied the legitimate winstat.exe process into the downloads folder on his system. He then ran process monitoring tool, procmon, to get a better understanding of what DLLs the EXE is looking for during execution.
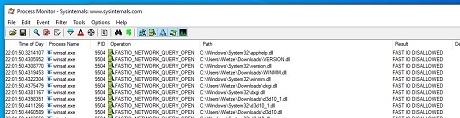 Process monitor showing accessed DLLs - source: wietzebeukema.nl
Process monitor showing accessed DLLs - source: wietzebeukema.nlThis allows us to identify all DLLs queried by each application, which will be all potential hijackable DLL candidates. But it does not automatically follow that all of these are also loaded (and therefore executed), explained the researcher.
The most reliable way to find out which DLLs are properly loaded is to compile our own version of the DLL and make it write to a unique file upon successfully loading. If we then repeat the above approach for all target executables and DLLs, it will result in a collection of files that tells us which DLLs are confirmed vulnerable to DLL hijacking.
What poses a challenge for the attacker, though, is compiling a custom version of DLL that can be launched by the executable, without any issues. To get a reliable understanding of a legitimate DLL structure, Beukema recommends using tools like DLL Export Viewer for analysis.
This tool provides insight into the DLL structure we are trying to recompile by enumerating all external functions names that would then be duplicated in a DLL Hijacking exploit.
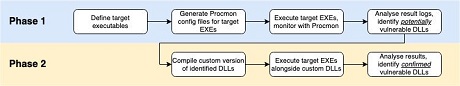 Approach to finding vulnerable executables - source: wietzebeukema.nl
Approach to finding vulnerable executables - source: wietzebeukema.nlThe researcher has provided a comprehensive list of libraries that are good candidates for hijacking attacks.
He added, these are not mere theoretical targets, these are tested and confirmed to be working. The list comprises 287 executables and 263 unique DLLs.
A CSV with a complete list of these libraries has been provided via
GitHub.
source