An Android malware strain camouflaged as a system app is used by threat actors to disable the Google Play Protect service, generate fake reviews, install malicious apps, show ads, and more.
The heavily obfuscated malware dubbed Trojan-Dropper.AndroidOS.Shopper.a uses a system icon and the ConfigAPKs name which closely resembles the name of a legitimate Android service responsible for app configuration the first time a device is booted.
"Trojan-Dropper.AndroidOS.Shopper.a was most widespread in Russia, where the largest share of infected users (28.46%) was recorded in October November 2019," Kaspersky Lab researcher Igor Golovin said. "Second place went to Brazil (18.70%) and third to India (14.23%)."
Malicious Play Store promotion servicesOnce it infects a victim's Android device, the malware downloads and decrypts the payload, then goes straight to information harvesting, collecting device info such as country, network type, vendor, smartphone model, email address, IMEI, and IMSI.
All this data is then exfiltrated to the operators' servers which will send back a series of commands to be run on the infected smartphone or tablet.
The attackers will utilize the Shopper.a Trojan to boost other malicious apps' ratings on the Play Store, post fake reviews on any apps' entries, install other apps from the Play Store or third-party app stores under the cover of an "invisible" window.
All this is done by abusing the Accessibility Service, a known tactic used by Android malware to perform a wide range of malicious activities without needing user interaction [1, 2, 3, 4]. If it has no permissions to access the service, the Trojan will use phishing to get them from the compromised device's owner.
The malware also disables the Google Play Protect mobile threat protection service, Google's built-in Android malware protection, so that it can go about its business undisturbed.
"Google Play Protect scans over 50 billion apps every day across more than two billion devices," according to the Android Security & Privacy 2018 Year In Review report published in March 2019.
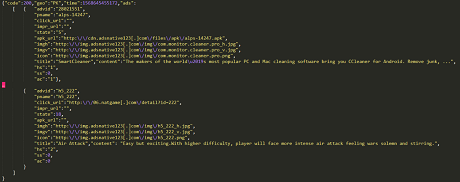 Shopper.a receiving command (Kaspersky Lab)
Shopper.a receiving command (Kaspersky Lab)"The lack of installation rights from third-party sources is no obstacle to the Trojan it gives itself the requisite permissions through Accessibility Service," Kaspersky Lab researcher Igor Golovin explained.
"With permission to use it, the malware has almost limitless possibilities for interacting with the system interface and apps. For instance, it can intercept data displayed on the screen, click buttons, and emulate user gestures."
Depending on what commands it receives from its masters, Shopper.a can perform one or more of the following tasks:
Open links received from the remote server in an invisible window (whereby the malware verifies that the user is connected to a mobile network).
After a certain number of screen unlocks, hide from the apps menu.
Check the availability of Accessibility Service rights and, if not granted, periodically issue a phishing request to the user to provide them.
Disable Google Play Protect.
Create shortcuts to advertised sites in the apps menu.
Download apps from the third-party market Apkpure[.]com and install them.
Open advertised apps on Google Play and click to install them.
Replace shortcuts to installed apps with shortcuts to advertised sites.
Post fake reviews supposedly from the Google Play user.
Show ads when the screen is unlocked.
Register users through their Google or Facebook account in several apps.
"Cybercriminals use Trojan-Dropper.AndroidOS.Shopper.a to boost certain apps rating and increase the number of installations and registrations," Golovin added.
"All this can be used, among other things, to dupe advertisers. Whats more, the Trojan can display advertising messages on the infected device, create shortcuts to ad sites, and perform other actions."
In related news, Google disclosed that Play Protect detected and removed around 1,700 applications infected with the Joker Android malware (also known as Bread) from the Play Store since the company started tracking this strain in early 2017.
To put things into perspective, while the Android Security & Privacy 2018 yearly review did not provide the exact number of removed malicious apps, 2017 one states that the company "took down more than 700,000 apps that violated the Google Play policies, 70% more than the apps taken down in 2016."
source